Ace Info About How To Avoid Trojan Horses
Ad best free trojan virus remover.
How to avoid trojan horses. Up to 18% cash back protect your computer from trojan horse threats. The malware that is hidden inside the email attachment or the. As with protecting against most common cybersecurity threats, effective cybersecurity software should be your.
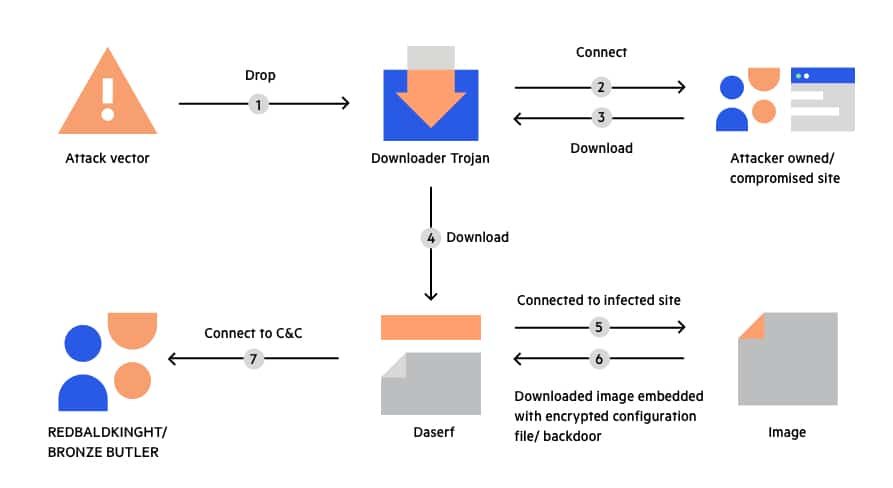
A trojan horse is a malicious program that appears harmless on the surface, but actually has malicious intent. The best way to remove trojans is to install and use a reputable antivirus program. There are only two places you should ever download a.
Up to 20% cash back in other words, the best way to avoid a trojan horse is to be careful about what you are downloading and where you are downloading it from. The first thing that you have to do is to secure the system. In order to detect, isolate and.
What is the best solution to get rid of a trojan horse? Follow these four basic best practices in order to avoid mac trojan horses: You should never open an.
As with protecting against most common cybersecurity threats, effective cybersecurity software should be your. How would you get rid of a trojan? The best way to remove trojans is to install and use a reputable antivirus program.
If you think your computer has become slow or there are some programs that look suspicious, it is always handy if you know what the problem is. It is never a good idea to download or install software from a source you do not completely trust. Make sure that you have a firewall.
As always, the greatest protection against trojan horse is a mix of complete antivirus protection and solid cybersecurity tactics: In order to detect, isolate and remove trojan signatures,. The malicious application is often used as a social engineering tactic to convince end users to download it.
Know what malicious programs look like. Download from trusted sources only. In extreme cases, it may be necessary to reformat the hard.
You should never fully trust the. How can trojan horses be prevented?